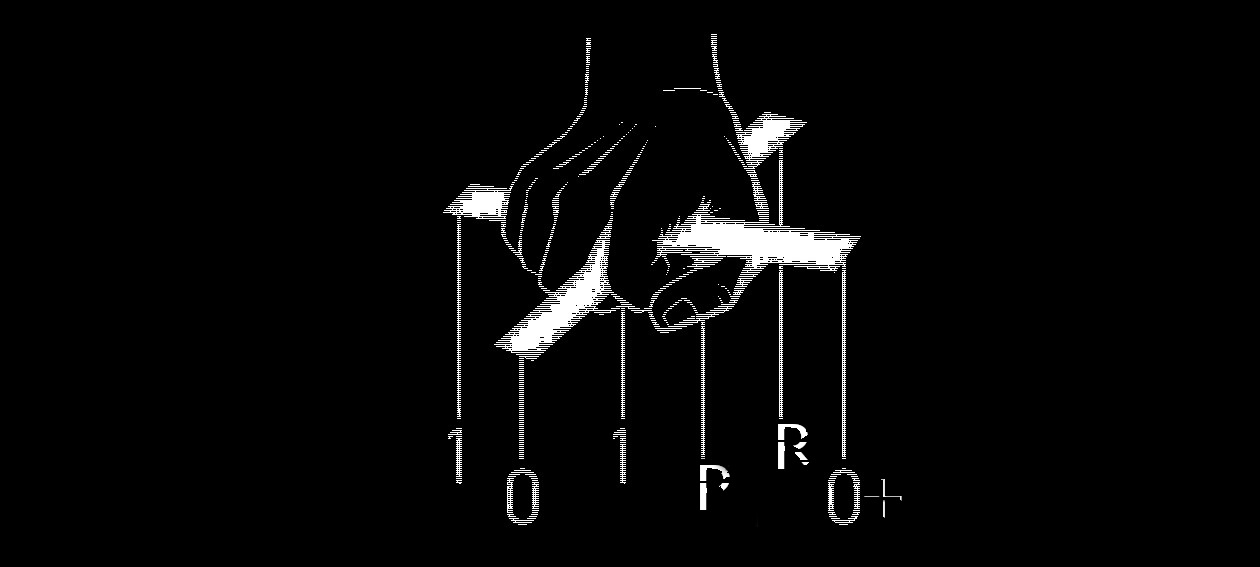
For our upcoming major version update we put all of our focus into enhancing the runtime evasion capabilities of the infected binaries.
A vast amount of updates were applied to our position independent code stubs, and two major features were implemented.
- Memory Scan Evasion
- This update brings the ability to encode/decode all the necessary stubs on the fly. This ensures that only the absolute minimal portion of our code will remain decoded in memory at all times.
- This feature also packs the ability to keep important information in our data structures, such as but not limited to function pointers, encoded for the entire lifetime of the process. All encoded data is fetched and decoded on the fly, while the original copy inside the data structures remains always encoded.
- Finally, all dynamically built strings are now cleared off the current thread’s stack memory after usage.
- Total Recall
This feature was implemented in order to further eradicate in-memory traces of our code under certain circumstances. There may be scenarios where none of the payloads will execute for various reasons such as, VM/DBG detection on process start, and/or failure to fetch remote AES keys for payload decryption. When this happens, this special feature will kick in and will clean-up all of our executable code from memory, as well as other memory areas that may store additional data. In short, this is an additional anti-analysis measure; especially against sandboxes that may provide memory dumps of the examined process.
The roadmap is still rich of features that we are looking to prioritise based on requests and functional requirements.
In the meantime, we are looking forward to make this build available to our customers.
We are on track for a Mid-April release.
Stay tuned!
kyREcon